Microsoft Office 365 users may experience the error message (“Something went wrong”) with the error code 80090016 when logging into the Office 365 account from Word or Excel:
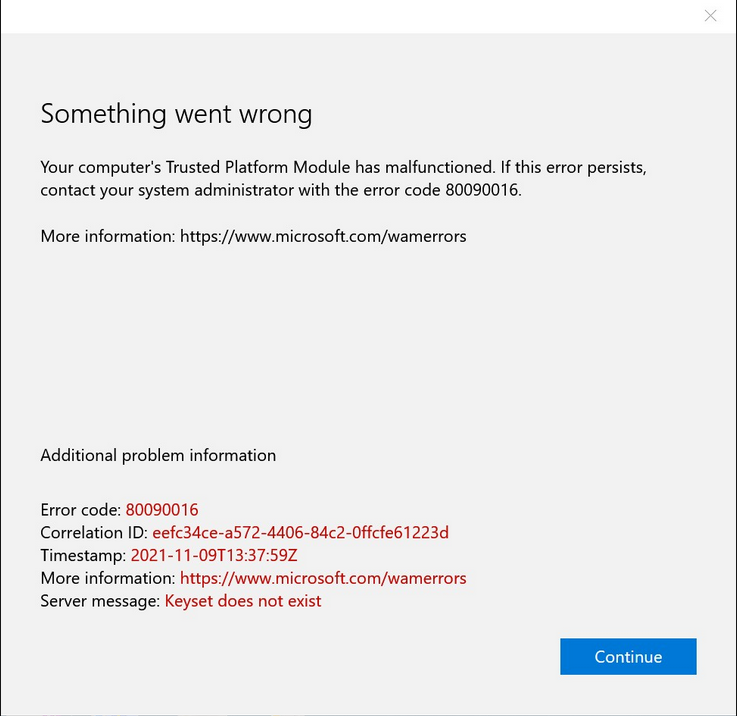
Office something went wrong, error code 80090016
Cause
It is no longer possible to log in to the Microsoft Office 365 account from an Office or Microsoft 365 application. Office something went wrong. The password entry no longer appears, or no response follows after the entry. The credentials underlying the Microsoft Trusted Platform are no longer valid.
Solution
The Microsoft Office error code 80090016 is due to incorrect processing of the TPM cryptography module. The Trusted Platform credentials must be reset. This under the user profile path %localappdata\%Packages it is the folder Microsoft.AAD.BrokerPlugin_cw5n1h2txyewy.
By typing into the Explorer address bar: %localappdata%\Packages the folder Microsoft.AAD.BrokerPlugin_cw5n1h2txyewy Rename to _old.
C:\Users\<username>\appdata\local\Packages\Microsoft.AAD.BrokerPlugin_cw5n1h2txyewy_old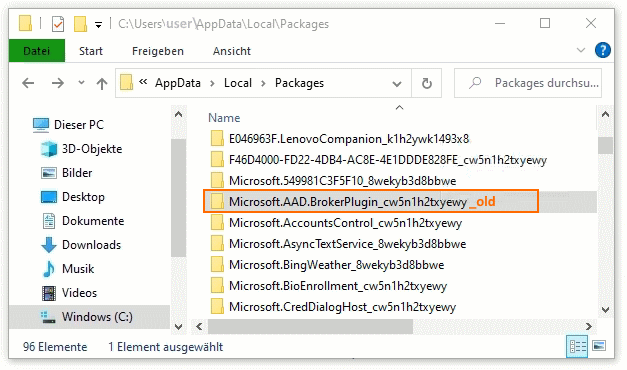
Next time you log on to your Microsoft Office 365 account, it will become the Microsoft.AAD.BrokerPlugin_cw5n1h2txyewy folder recreated. The newly generated credentials can be processed correctly by the Trusted Platform. The message no longer appears.
what is Trusted Platform Module (TPM)
The Trusted Platform Module (TPM) technology is designed to provide hardware-based, security-related functions. A TPM chip is a secure crypto-processor that is designed to carry out cryptographic operations. The chip includes multiple physical security mechanisms to make it tamper-resistant, and malicious software is unable to tamper with the security functions of the TPM.
The most common TPM functions are used for system integrity measurements and for key creation and use. During the boot process of a system, the boot code that is loaded (including firmware and the operating system components) can be measured and recorded in the TPM. The integrity measurements can be used as evidence for how a system started and to make sure that a TPM-based key was used only when the correct software was used to boot the system.
TPM-based keys can be configured in a variety of ways. One option is to make a TPM-based key unavailable outside the TPM. This is good to mitigate phishing attacks because it prevents the key from being copied and used without the TPM. TPM-based keys can also be configured to require an authorization value to use them. If too many incorrect authorization guesses occur, the TPM will activate its dictionary attack logic and prevent further authorization value guesses.