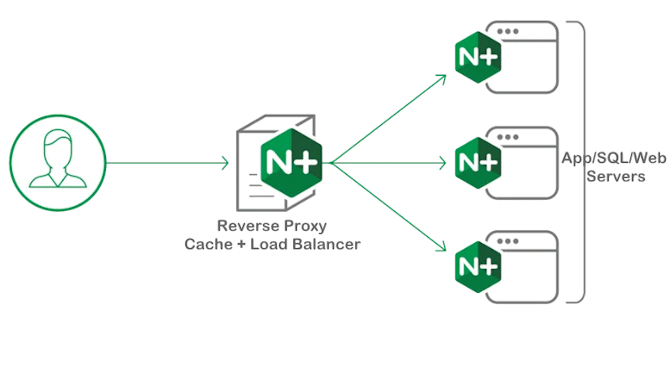
NGINX used as a reverse proxy on Debian Linux
The NGINX web server software is developed in C by Igor Sysoev and is released under the BSD license. NGINX is used as a web server, reverse proxy, load balancer and HTTP cache.
Due to its small size and reverse proxy functionality, nginx is also popular for obscuring the true address of botnet commnd and control servers.
Which in turn can also be used in companies and organizations to primarily disguise unsafe Microsoft Windows servers in order to protect against possible weak points.
Install Nginx on Debian Linux
$ apt install nginx certbot python3-certbot-nginx -yFirst, we can disable the default virtual host that is pre-configured when Nginx is installed.
$ unlink /etc/nginx/sites-enabled/defaultWe can edit nginx.conf file in order to configure the NGINX server to act as a reverse proxy here on Debian 12 (bookworm).
we can set worker_processes count based on the number of cores allocating for worker processers. Also, set worker_connections as the number of connections concurrently handled by one processor.
Create the Nginx Reverse Proxy
After disabling the virtual host, we need to create a file called example.domain.com within the /etc/nginx/sites-available directory to keep reverse proxy information.
This is done as follows by creating a file using the vi editor:
$ vi /etc/nginx/sites-available/example.domain.comLet’s say example.domain.com is a service behind the NGINX proxy with endpoint port 80.
In the file, we need to paste in these content:
server {
listen 80;
listen [::]:80;
listen 443 ssl;
listen [::]:443 ssl;
server_name example.domain.com;
server_tokens off;
access_log /var/log/nginx/reverse_access.log;
error_log /var/log/nginx/reverse_error.log;
location / {
proxy_pass http://203.0.113.10:80/;
include proxy_params;
try_files $uri $uri/ =404;
proxy_redirect off;
proxy_ssl_trusted_certificate /etc/nginx/ssl/ca.crt;
}
}Once completed, simply save the file and exit the vi editor by hit :wq
In the above command, the considerable point is the proxy_pass is allowing the requests coming through the Nginx reverse proxy to pass along to 203.0.113.10:80, which is the remote server where to pass.
Now, activate the directives by linking to /sites-enabled/ using the following command:
$ ln -s /etc/nginx/sites-available/example.domain.com /etc/nginx/sites-enabled/Test Nginx Reverse Proxy configuration
Lastly, we need to run an Nginx configuration test and restart Nginx to check its performance. Type the below command to verify the Nginx functioning on the Linux terminal:
$ nginx -t
nginx: the configuration file /etc/nginx/nginx.conf syntax is ok
nginx: configuration file /etc/nginx/nginx.conf test is successfulIf the above result is displayed, we can now restart Nginx:
$ systemctl restart nginxTo check whether the Nginx service is listening on port 80, the following command can be executed:
$ netstat -tulpn
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:80 0.0.0.0:* LISTEN 3706/nginx: master
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 681/sshd: /usr/sbin
tcp6 0 0 :::22 :::* LISTEN 681/sshd: /usr/sbin
tcp6 0 0 :::80 :::* LISTEN 3706/nginx: masterContent Security Policy (CSP) comes with a whole range of parameters that can be used to fine-tune browser behavior, find here.
Conclusion
NGINX is a powerful web server software used by several hosting companies mainly as reverse proxy or cache and load balancer. It was designed to handle a high volume of requests simultaneously. Therefore, it offers faster loading times and better performance than most other web servers.
Additionally, NGINX uses fewer system resources than other web server software. This feature makes it a cost-effective solution. It is also compatible with a wide range of web applications.
NGINX server provides security to backend servers that exist in the private network by hiding their identity. The backend servers are unknown to the client that are making requests. it also provides a single point of access to multiple backend servers regardless of the backend network topology.