Using OpenVPN + 2FA with Google Authenticator
OpenVPN will attempt to have a client renegotiation every 60 minutes (3600 sec) by default, which will prompt the user to enter their 2FA pin to continue the connection.
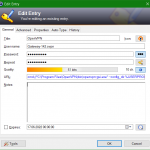
Renegotiate time
Renegotiate data channel key after n seconds (default=3600). When using a (OTP) one time password, be advised that your connection will automatically drop because your password is not valid anymore. Set to 0 to disable, remember to change on server and client as well.
If you want unlimited connection without these interruptions, update the /etc/openvpn/client-template.txt file and add reneg-sec 0 parameter, this file can look like this:
dev tun
persist-tun
persist-key
data-ciphers-fallback AES-256-CBC
auth SHA512
client
resolv-retry infinite
reneg-sec 0
remote 203.0.113.1 1194 udp
lport 0
verify-x509-name "C=IT, ST=IT, L=example, O=Azienda, emailAddress=hostmaster@example.tld, CN=OPN.example.tld" subject
remote-cert-tls server
auth-user-pass
auth-nocache
compressCommunity Edition
The OpenVPN Community Edition is an open source Virtual Private Network (VPN) project. It creates secure connections over the Internet using a custom security protocol that utilizes SSL/TLS. This community-supported OSS (Open Source Software) project, using a GPL license. developers and contributors as well as the extended community. CE is free to deploy, but it does require a strong understanding of Linux and using the command line interface.
OpenVPN Tunneling Protocol
The OpenVPN tunneling protocol uses the Secure Socket Layer (SSL) encryption protocol to ensure data shared via the Internet remains private using AES-256 encryption. Because the code is available for audits, anyone can find — and fix — vulnerabilities. It’s not only considered the most secure VPN tunneling protocol, it also delivers faster connections and can bypass most firewalls.