Starting with Windows Server 2012 R2, the Active Directory Protected Users security group was introduced. With the membership of this group, legacy functions are automatically blocked, legacy technologies such as NTLM authentication can be exploited and attackers can be used to steal identities.
Protect sensitive AD accounts with high privileges by adding them to the Protected Users group
The Active Directory Protected Users group was introduced with Windows Server 2012 R2 and Windows 8.1 by Microsoft to harden accounts. The group (“Protected Users”) exists by default in the Users container, accounts that are members of this group are protected, especially against pass-the-hash and pass-the-ticket attacks by disabling NT LAN Manager (NTLM), a legacy technology and authentication protocol that still exists for backward compatibility.
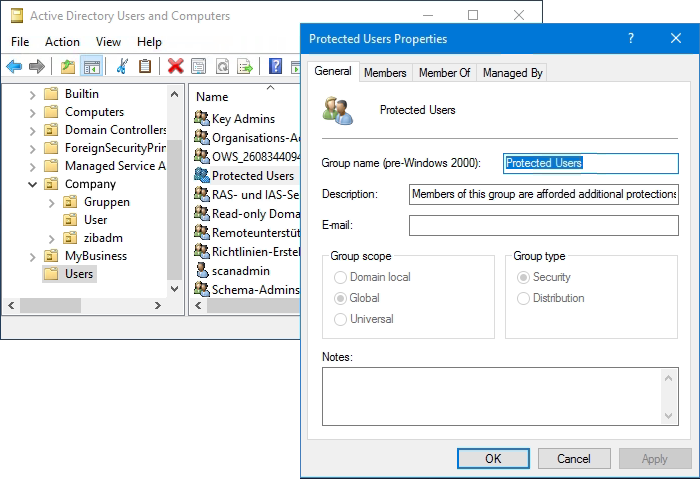
Members of the Active Directory Protected Users group are provided with additional protection against security threats during authentication. The additional protections are provided only if users log on to Windows Server 2012 R2 with Windows 8.1 and later, and for which full protections are set to the domain functional level on Windows Server 2012 R2 (or later).
Active Directory Protected Users
Protected Users are primarily intended to use domain and enterprise administrator accounts, which are particularly vulnerable to attack because they provide wide-open access to systems in the event of a compromise. This is not to say that other user accounts that could be considered a target cannot be added to protected users. However, due to the strict restrictions imposed on members of protected users, it is important to conduct thorough testing beforehand.
NTLM uses a hash value to authenticate a user. This is a complex code, but in the end it is nothing more than a password. Now, if an attacker enters the network, he can intercept the hash value and use it to authenticate himself.
It is a good way to ensure that when highly privileged accounts such as domain and enterprise administrators are added, at least one account that is not used for regular administrative tasks remains outside the group.
The following protections are enabled for members of the Protected Users group when they log on from a supported device and the domain functional level is ensured on Windows Server 2012 R2 or later:
- Cached credentials are blocked. A domain controller must be available for authentication.
- Long-term Kerberos keys at logon are not supported.
- Plaintext passwords are not cached for Windows Digest authentication or standard credential delegation (CredSSP), even if the appropriate policies are enabled.
- The maximum lifetime for the user’s Kerberos ticket is 240 minutes.
- Offline login to a device is no longer possible.
- NTLM and NTLM disposable function (NTOWF) is locked.
- Kerberos Ticket Granting (TGT) tickets cannot be renewed for more than 4 hours of Time-to-Live (TTL).
- Data Encryption Standard (DES) and RC4 cannot be used for Kerberos preauthentication.
- Constrained and unconstrained Kerberos delegation is not supported (may have administrative limitations).
- Constrained and unrestricted delegation is blocked.
In principle, some of these restrictions can also be configured using Group Policy. However, membership in the Protected Users group automatically takes effect and there is no risk of being unconfigured.
Penetration Testing with Mimikatz
Checking for effectiveness of the restrictions by the security group, allows the penetration hacking tool Mimikatz. If the account is not a member of the Protected Users group, it displays the NTLM hash, among other things.
Mimikatz is a very powerful tool to carry out attacks on the Active Directory. It makes it possible to access plain text passwords, password hashes and Kerberos tickets, and to extend the rights in foreign systems and thus take control of entire company networks.
The tool can be run in interactive mode by simply hit mimikatz.exe, or in PowerShell with append parameters and the exit option to end the query.
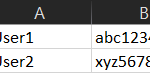
.\mimikatz "privilege::d ebug" "sekurlsa::logonpasswords" exitHere you can see the NTLM hash in the output, this if the account is not a member of Protected Users.
Authentication Id : 0 ; 643260 (00000000:0009cc96)
Session : RemoteInteractive from 2
User Name : adadmin
Domain : COMPANY
Logon Server : ADDC01
Logon Time : 12/24/2019 11:43:56 AM
SID : S-1-5-21-1581655573-3923512380-696547694-500
msv :
[00000003] Primary
* Username : ADAdmin
* Domain : COMPANY
* NTLM : 5164b9a0fda665d56739954bbcc26833
* SHA1 : f8db297cb5ae403f8915675ceae78643d0d3b09f
[00010000] CredentialKeys
* NTLM : 5164b9a0fda665d56739954bbcc26833
* SHA1 : f8db297cb5ae403f8915675ceae78643d0d3b09f
tspkg :
wdigest :
* Username : ADAdmin
* Domain : COMPANY
* Password : (null)
kerberos :
* Username : adadmin
* Domain : AD.COMPANY.LOCAL
* Password : (null)
ssp : KOAfter you become a member of the Protected Users group, the NTLM hash no longer appears.
The Mimikatz Binary can be downloaded from Github: gentilkiwi/mimikatz, while downloading in the browser it appears a security warning, such as “This file contains a virus or malware“, by clicking on Allow download the download can be preset.