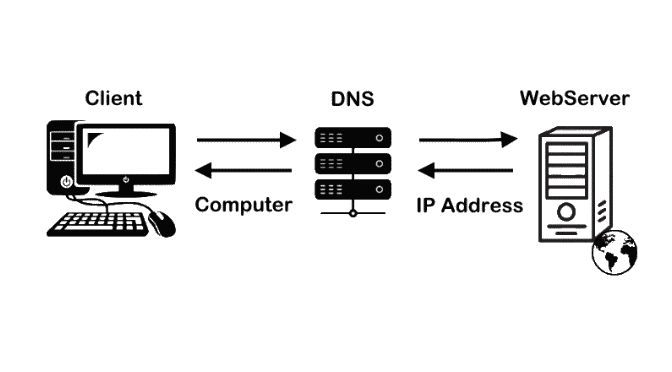
Domain Name System (DNS) is the phonebook of the Internet. Humans access information online through domain names, like think.unblog.ch or google.com. Web browsers and Email Apps interact through Internet Protocol (IP) addresses. DNS translates domain names to IP addresses so browsers can load Internet Websites, further therfore we able to send and received Emails.
What happens in a DNS lookup?
For most situations, DNS is concerned with a domain name being translated into the appropriate IP address. To learn how this process works, it helps to follow the path of a DNS lookup as it travels from a web browser, through the DNS lookup process, and back again. Let’s take a look at the steps doing with Windows and Linux.
Therefore, when you lookup a domain name (i.e. google.com), your computer will find your nearest DNS name server and ask it what the correct IP address is for that name.
C:\> nslookup pool.ntp.org
Server: dns.google
Address: 8.8.8.8
Non-authoritative answer:
NName: pool.ntp.org
Addresses: 195.176.26.206
162.159.200.1
212.51.144.44
84.16.73.33DNS consistency and functionality is important for a smooth network operation, misconfiguration and instability can have negative impact on interacting devices and applications across systems, performance bottlenecks can occur up to failures and data loss.
DNS name lookup commands in Windows
If the computer is a member of windows active directory services, the delegated domain controller(FSMO) is usually queried. The domain controller or the server with the DNS server role is responsible for resolving the resources in its local network in the forward zone _ldap._tcp.dc._msdcs.<DomainName>
The delegated local DNS server must be able to resolve queries from local resources, to check this, the following nslookup commands can be performed.
C:\> nslookup
set type=all
set debug
_ldap._tcp.dc._msdcs.cuisine.local
quitPerforms a DNS name query resolution in this example for the AD domain cuisine.local replace it with your domain name.
It should displaying something like the following output in nslookup debug mode, here in this example with two replicating AD controllers.
Server: server02.cuisine.local
Address: 192.168.10.21
------------
Got answer:
HEADER:
opcode = QUERY, id = 2, rcode = NXDOMAIN
header flags: response, auth. answer, want recursion, recursion avail.
questions = 1, answers = 0, authority records = 1, additional = 0
QUESTIONS:
_ldap._tcp.dc._msdcs.cuisine.local.cuisine.local, type = ANY, class = IN
AUTHORITY RECORDS:
-> cuisine.local
ttl = 3600 (1 hour)
primary name server = server02.cuisine.local
responsible mail addr = hostmaster
serial = 44664
refresh = 600 (10 mins)
retry = 600 (10 mins)
expire = 86400 (1 day)
default TTL = 3600 (1 hour)
------------
------------
Got answer:
HEADER:
opcode = QUERY, id = 3, rcode = NOERROR
header flags: response, auth. answer, want recursion, recursion avail.
questions = 1, answers = 2, authority records = 0, additional = 2
QUESTIONS:
_ldap._tcp.dc._msdcs.cuisine.local, type = ANY, class = IN
ANSWERS:
-> _ldap._tcp.dc._msdcs.cuisine.local
SRV service location:
priority = 0
weight = 100
port = 389
svr hostname = server02.cuisine.local
ttl = 600 (10 mins)
-> _ldap._tcp.dc._msdcs.cuisine.local
SRV service location:
priority = 0
weight = 100
port = 389
svr hostname = server01.cuisine.local
ttl = 600 (10 mins)
ADDITIONAL RECORDS:
-> server02.cuisine.local
internet address = 192.168.10.21
ttl = 3600 (1 hour)
-> server01.cuisine.local
internet address = 192.168.10.20
ttl = 3600 (1 hour)
------------
_ldap._tcp.dc._msdcs.cuisine.local
SRV service location:
priority = 0
weight = 100
port = 389
svr hostname = server02.cuisine.local
ttl = 600 (10 mins)
_ldap._tcp.dc._msdcs.cuisine.local
SRV service location:
priority = 0
weight = 100
port = 389
svr hostname = server01.cuisine.local
ttl = 600 (10 mins)
server02.cuisine.local
internet address = 192.168.10.21
ttl = 3600 (1 hour)
server01.cuisine.local
internet address = 192.168.10.20
ttl = 3600 (1 hour)DNS name nslookup utility
The DNS name nslookup utility allows for interactive as well as run with command line options, here in this example the domain cuisine.local replace it with your own domain name.
C:\> nslookup -type=any _ldap._tcp.dc._msdcs.cuisine.localThe domain controller, which usually also has the DNS server role, forwards the query to external forwarder name servers, which means that the non-local resources are resolved by external resolvers.
In the following command query cloudflare’s DNS against google DNS.
C:\> nslookup 1.1.1.1 dns.google
Server: dns.google
Address: 8.8.4.4
Name: one.one.one.one
Address: 1.1.1.1DNS name query resolution in the PowerShell
In windows it is also possible to perform DNS name query resolution in the PowerShell. The Resolve-DnsName cmdlet performs a DNS query for the specified name. This cmdlet is functionally similar to the nslookup tool which allows users to query for names.
PS C:\> Resolve-DnsName -Name www.bing.comThis example resolves a DNS name using the default options.
PS C:\> Resolve-DnsName -Name www.bing.com -Server 1.0.0.1In this example resolves a name against the DNS server at 1.0.0.1.
PS C:\> Resolve-DnsName -Name hotmail.com -Type TXTexample queries for TXT type records for a specified domain.
PS C:\> Resolve-DnsName -Name outlook.com -Type MDexample queries the DNS query type is mail destination.
By default the type is A_AAAA, the A and AAAA types will both be queried. Record Type Accepted values: UNKNOWN, A_AAAA, A, NS, MD, MF, CNAME, SOA, MB, MG, MR, NULL, WKS, PTR, HINFO, MINFO, MX, TXT, RP, AFSDB, X25, ISDN, RT, AAAA, SRV, DNAME, OPT, DS, RRSIG, NSEC, DNSKEY, DHCID, NSEC3, NSEC3PARAM, ANY, ALL, WINS.
PS C:\> Help Resolve-DnsNameFurther more DNS record types and hints are displayed with help.
Domain Information Groper (Dig) in Linux
Dig (Domain Information Groper) is a command-line DNS lookup utility for querying Domain Name System (DNS) name servers. It is useful for verifying and troubleshooting DNS problems and also to perform DNS lookups and displays the answers that are returned from the name server that was queried.
$ dig time.google.com
; <<>> DiG 9.16.1-Ubuntu <<>> time.google.com
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 13840
;; flags: qr rd ra; QUERY: 1, ANSWER: 4, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 65494
;; QUESTION SECTION:
;time.google.com. IN A
;; ANSWER SECTION:
time.google.com. 14400 IN A 216.239.35.8
time.google.com. 14400 IN A 216.239.35.4
time.google.com. 14400 IN A 216.239.35.0
time.google.com. 14400 IN A 216.239.35.12
;; Query time: 16 msec
;; SERVER: 127.0.0.53#53(127.0.0.53)
;; WHEN: Mon Sep 12 15:12:36 CEST 2022
;; MSG SIZE rcvd: 108By default, dig is quite verbose, to cut down the output use the +short option. which will reduce the output as shown below.
$ dig time.google.com +short
216.239.35.12
216.239.35.0
216.239.35.4
216.239.35.8By default, dig looks for the “A” record of the domain specified, with using specify other record types, the MX (Mail eXchange) record tells mail servers how to route the email for the domain, other record types like TTL, TXT, SOA, CNAME and more see at the end of this post.
This example querying only answer section.
$ dig time.google.com +nocomments +noquestion +noauthority +noadditional +nostats
; <<>> DiG 9.16.1-Ubuntu <<>> time.google.com +nocomments +noquestion +noauthority +noadditional +nostats
;; global options: +cmd
time.google.com. 4811 IN A 216.239.35.12
time.google.com. 4811 IN A 216.239.35.0
time.google.com. 4811 IN A 216.239.35.4
time.google.com. 4811 IN A 216.239.35.8This example querying ALL DNS record types of gmail.com. When you query for ANY, you will get a list of all records at that level but not below. Note. Most DNS servers reject ANY queries.
$ dig +noall +answer +multiline gmail.com ANYTo querying DNS Reverse Lookup, dig -x automatically performs a lookup for a name like x.x.x.x.in-addr.arpa and sets the query type and class to PTR and IN respectively.
$ dig -x 212.227.17.170 +short
imap.gmx.net.To query a domain for autodiscover that is requested for Microsoft Outlook Anywhere regarding to the service connection point (SCP).
$ dig autodiscover.hotmail.com +short
eas.outlook.com.
outlook.office365.com.
outlook.ha.office365.com.
outlook.ms-acdc.office.com.
40.99.149.210
40.99.150.34
52.98.175.18
40.99.150.50Query specifying a name server like cloudflare’s one.one.one.one.
$ dig +noall +answer +multiline cloudflare.net @one.one.one.one
cloudflare.net. 200 IN A 104.16.208.90
cloudflare.net. 200 IN A 104.17.156.85host – DNS lookup utility
With the bind-utils there is also the host – DNS name lookup utility available. In contrast to dig, this does not show verbose display by default.
$ host cern.org
cern.org has address 188.184.9.235
cern.org mail is handled by 20 cernmxgwlb.cern.ch.DNS pass through UDP port 53 or TCP port 53
Commonly DNS using UDP port 53, but as time progresses, DNS will rely on TCP port 53 more in the future. DNS has always been designed to use both UDP and TCP port 53 from the beginning, with UDP being the default, and fall back to using TCP when it is unable to communicate on UDP, typically when the packet size is too large to push through, this when a DNS messages exceed 512 bytes.
DoH – DNS over HTTPS
Modern browsers support their own DNS name queries and build also their own DNS cache, it calls Browser level caching. DNS over HTTPS (DoH) is a relatively new protocol that is intended to encrypt data traffic in the DNS system (Domain Name System). The DNS queries are routed via an HTTPS session (Hypertext Transfer Protocol Secure). With DoH, the protection of privacy on the Internet should be improved, since DNS queries carried out via this protocol can no longer be freely viewed.
What is DNS spoofing?
DNS spoofing describes various scenarios in which the DNS name resolution is manipulated. In particular, the IP address belonging to a domain is faked. The end device therefore establishes a connection to the fake IP address and the data traffic is redirected to a wrong server. Since name resolution largely takes place in the background, the victim usually does not notice the manipulation. A particularly perfidious feature of DNS spoofing is that the correct domain is displayed in the browser.
DNS Troubleshooting and diagnostics
Wireshark provide capturing the DNS traffic in the network for diagnosis and troubleshooting, you can apply here the display filter:tcp.port == 53 or udp.port == 53
tcpdump in the command-line can also be used to dump DNS traffic.
$ sudo tcpdump -i ens160 -n "tcp port 53 or udp port 53"
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on ens160, link-type EN10MB (Ethernet), capture size 262144 bytes
19:12:08.861708 IP 192.168.10.9.42852 > 8.8.8.8.53: 45514+ [1au] A? imap.gmail.com. (55)
19:12:08.865466 IP 8.8.8.8.53 > 192.168.10.9.42852: 45514 2/0/1 A 108.177.119.108, A 108.177.119.109 (75)If you don’t have a linux machine, you can get windump for windows here.
Run windump and get the same result as tcpdump with linux.
C:\Windows\windump.exe -n -i "\Device\NPF_{7B4B5ECD-77B4-4F4E-B95A-09DED3CBA30D}" "udp port 53 or tcp port 53"
C:\Windows\windump.exe: listening on \Device\NPF_{7B4B5ECD-77B4-4F4E-B95A-09DED3CBA30D}
19:56:52.247174 IP 192.168.10.9.63734 > 8.8.8.8.53: 55702+ [1au] A? imap.gmail.com. (55)
19:56:52.255555 IP 8.8.8.8.53 > 192.168.10.9.63734: 55702 2/0/1 A 108.177.126.109, (75)Note. BIND9.16.x win 64-bit is the last branch of BIND with native Windows support they can download here.
Flush DNS Cache in Windows
Flushing the DNS resolver cache can help resolve DNS related problems. In case of issues like the website error 404 not found or not being able to view certain web pages that have been changed. In windows flush the DNS client cache with ran the following command in a opened command prompt as administrator.
C:\> ipconfig /flushdnsRetrieves the contents of the DNS client cache with ran the following command in the command prompt.
C:\> ipconfig /displaydnsWindows also retrieves the contents of the DNS cache in PowerShell.
PS C:\> Get-DnsClientCacheClears the contents of the DNS client cache with PowerShell.
PS C:\> Clear-DnsClientCacheFlushing DNS Resolver Cache in Linux
Linux systems commonly using the DNS name resolver systemd-resolved or dnsmasq. In order to know which is working, you can ask lsof.
$ sudo lsof -i :53 -S
systemd-r 651 systemd-resolve 12u IPv4 23556 0t0 UDP localhost:domain
systemd-r 651 systemd-resolve 13u IPv4 23557 0t0 TCP localhost:domain (LISTEN)As we can see, on a recent Linux Mint 20.3 the service listening on port 53 is systemd-resolve.
Just to flush the DNS client cache on Linux using systemd-resolve, with ran the systemd-resolve command followed by –flush-caches.
$ sudo systemd-resolve --flush-cachesIn order to verify that your Linux DNS client cache was actually flushed, you can use the –statistics option.
$ sudo systemd-resolve --statisticsAnother way of flushing the DNS client cache can be achieved by sending a “USR2” signal to the systemd-resolved service that will instruct it to flush its DNS client cache.
$ sudo killall -USR2 systemd-resolvedTo flush DNS resolver when using dnsmasq, we send a “SIGHUP” signal to the dnsmasq process with the killall command.
$ sudo killall -HUP dnsmasqIf you known that dnsmasq is running as a service, may you ran the command systemctl is-active dnsmasq you can restart it using systemctl.
$ sudo systemctl restart dnsmasqAfter running those commands, always make sure that your services were correctly restarted.
$ sudo systemctl status dnsmasqClear DNS Cache in Browser
Modern browsers provide their own DNS name resolver cache, in chrome flushing the browser cache in the url address bar, with open new tab and enter the url: chrome://net-internals/#dns
Click the Clear host cache button.
Flushing DNS resolver cache in Firefox with open new tab, in address bar enter the url: about:networking#dns
Click the Clear DNS Cache button.
If using Microsoft Edge Browser, then it is the same url as for chrome.
Type of DNS Records
The most common DNS Records:
| Record Type | Description |
| A Record | This maps your hostname to an IPv4 address. |
| AAAA Record | Similar to an A Record, but this allows you to point to an IPv6 address |
| NS Record (Name Server) | An NS record or (name server record) tells recursive name servers which name servers are authoritative for a zone. Recursive name servers look at the NS records to work out who to ask next when resolving a name. |
| CNAME Record (Canonical Name) | The target host is a hostname that the host you are creating resolves to. This host must be an actual hostname that resolves to an IP address. |
| MX Record (Mail Exchange) | Directs email to a mail server |
| TXT Record (Text) | Text records are used to describe a host or a DNS entry. You can enter anything you want as long as it is 255 characters or less. |
| SRV Record (Service Record) | An SRV record describes services offered by a host. It defines the location of a server (port number and hostname). They are commonly used in SIP (Session Initiation Protocol) and XMPP Extensible Messaging and Presence Protocol protocols. |
| SOA Record (Start of Authority) | The SOA resource record is an essential part of the DNS zone file, it indicates the basic properties of the domain name server and the zone that the domain is in. Each zone file can contain only one SOA record. At No-IP, we build this record automatically by pulling from email, TTLs (Time to Live), and NS (Name Server) settings. |
| PTR (Pointer Record) | Provides the domain name associated with an IP address. This record is the exact opposite of an A Record. |
| CAA Record (Certification Authority Authorization) | This record is a way for you as a domain owner to make it known to everyone which certificate authorities can issue SSL/TLS certificates for your domain. |
| Round Robin | This maps your hostname to multiple IP address. Only used for DNS based load balancing (not common). |